On April 28, 2021, Uranium Finance lost over $50 million in one morning. The attacker took advantage of the vulnerabilities present between pairs of smart contracts. After sending the minimum amount of tokens, they drained numerous liquidity pools in the BSC system.
This is a glaring example of the hacking that takes place in DeFi on a daily basis. To avoid losing hard-earned money, you should know how to identify fraudulent activities and therefore protect yourself in advance.
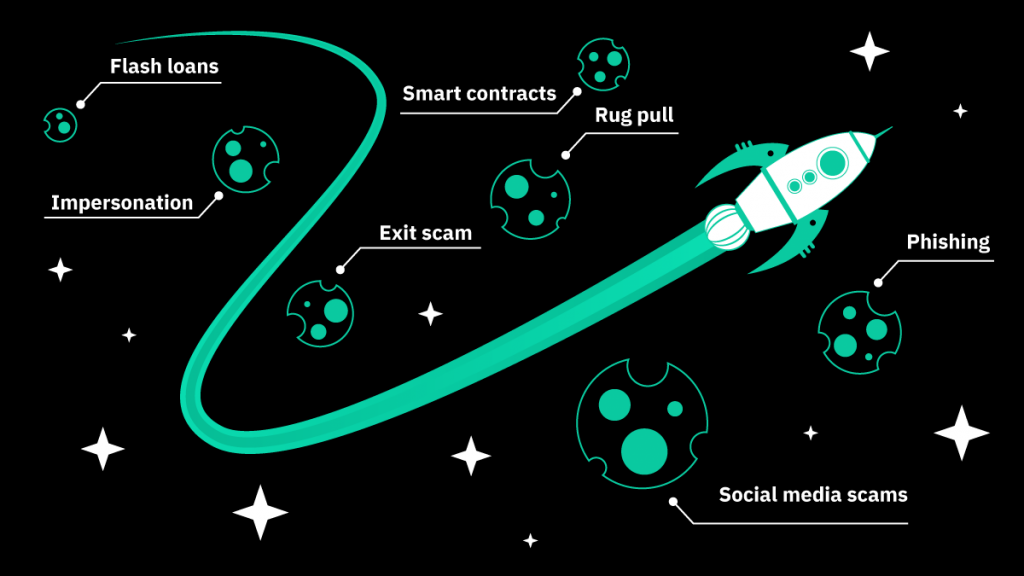
Scam and Hacking in DeFi: Main Types
Back in 2017, scammers launched new cryptocurrencies with promising concepts, raised funds during ICOs, and disappeared shortly thereafter, leaving their investors with abandoned projects. These days, tokens can be issued through IFO, IAO, and IEO. However, fraudulent schemes have also evolved. Here are the most popular scams in DeFi today:
Smart contracts. Hackers identify vulnerabilities in smart contracts, hack the code, and drain liquidity from the liquidity pools. This is what happened to Uranium Finance: attackers identified an unfixed math bug in the smart contracts and hacked them.
Rug pull. Scammers hold considerable numbers of tokens in liquidity pools, and once the prices of these tokens reach a certain height, they dump them in the market and leave. This is a common problem for DeFi: Meerkat Finance was recently rug pulled for $31 million.
Flash loans. An instantaneous, unsecured and uncollateralized large-sum transaction between a borrower and a lender during which scammers quickly profit from arbitrage opportunities. This is how Harvest Finance was exploited: the attacker drained $33.8 million and returned only $2.5 million in October 2020.
Exit scam. Scammers raise money on fake projects and disappear with this money shortly thereafter. They generally start by presenting a promising concept, followed by heavy advertising and hard-to-resist promises.
Impersonation. A scammer builds long-term trust with a victim and convinces the latter to invest. The scenario that plays out involves heavy preliminary research, presenting oneself as a representative of a reputable company, and pitching a brilliant idea.
Phishing. This refers to sending fake links to other websites that defraud funds. Scammers can ask for private keys, offer to invest on an individual’s behalf, or blackmail them.
Social media scams. These scams involve creating social media hype to raise funds. This is what happened when the Twitter accounts of Elon Musk, Bill Gates, Warren Buffett, and others were hacked in July 2020. Scammers posted the links to their blockchain addresses on the accounts of these opinion leaders, convinced their followers to invest, and raised more than $100,000.
User Risks of Scam in DeFi
- You can’t recover your funds: there is no “police” to approach.
- You can’t rely on security audits to fully evaluate the project quality.
- It’s not always possible to detect the identify project founders and developers.
- It’s hard to prosecute scammers: the legal base is not yet well-developed.

7 Things You Can Do to Protect Your Investment from Scammers in DeFi
1. Research the project. Study the data yourself until you feel comfortable with investing. Check the white paper and evaluate the project design and its profitability. It should have a bare-bones working model and make no unrealistic promises.
2. Check the smart contract’s code. If the smart contracts are upgradable, developers can use admin keys and change them anytime. Scammers may also use other vulnerabilities within the smart contract to withdraw all liquidity from the project.
3. Keep your private keys safe. Don’t reveal your private keys to anybody, be that a stranger or a person you trust.
4. Find project founders in social media. If possible, check the project team’s credentials, work experience, and connections. (e.g. of Confido’s founders) or use deepfake videos (e.g. using DeTrade Fund CEO’s image). If you notice something suspicious, consider it as a red flag. However, you should remember that not all projects whose founders prefer to stay in the shadows are scams.
5. Check tokens allocation and distribution. Stay away from big promotions of new coins, heavy advertising, and huge amounts of free tokens. If you’ve noticed suspicious transactions, try to stop them by complaining to centralized exchanges. In October 2020, Binance protected its users from an exit scam attempted by the DeFi project Wine Swap and ultimately prevented a loss of $345,000.
6. Double-check each offer. Be financially aware so that you do not fall victim to unrealistic promises. To protect yourself from phishing scams, check the syntax, encryption, and verify each email address and website link belonging to the said company before clicking.
7. Communicate on verified social media channels only. Scammers can contact you directly, pretending to be a representative of a team or a project bot, and ask you for money or private keys. Protect yourself by communicating in official groups only.

Checklist to a Trustworthy DeFi Project:
- Clear and original white paper
- Open-source project with a code on Github or Gitlab
- Founders have a good reputation in the crypto community
- The project has verified connections and partnerships
- Communication takes place on official social media channels only
- Nobody asks for your private keys
- A working model and the project’s profitability are easy to find and realistic
- No record of a huge coin holding in their transaction history
- No loud advertisement campaigns for fundraising
- Security audit conducted by external developers
- Project’s workers don’t have suspicious past activity records
Always consider the broad picture before making a single investment step. Be safe!