To put it simply, a crypto wallet is a tool that is managing your keys and allowing interaction with a Blockchain network. All wallets can be split into three categories: software, hardware, and paper ones. When focusing on their work mechanism, they are usually divided into “hot” or “cold” ones.
There are also custodial wallets. In this case, your keys are managed by a third-party “trusted” service. We won’t discuss this type.
Wallets’ examples:
- Hardware Wallets: Trezor, Ledger;
- Desktop Wallets: GalleonWallet, Bitcoin Core, Electrum;
- Mobile Wallets: AirGap, TrustWallet, ZenGo;
- Web Wallets: ThanosWallet, TezBox, MagnumWallet, MetaMask, MyEtherWallet.
Hot or Cold Wallet?
As was mentioned, wallets for cryptocurrencies are usually either “hot” or “cold” depending on whether a wallet has the ability to connect to the network.
Cold Wallets
Cold wallets are wallets that have NO internet connection. It makes them more resistant to hacking. There are some examples of such wallets:
- Hardware wallets, i.e. the separate physical e-device;
- CLI wallets, or console program;
- Paper wallets, namely piece of paper on which the public and private keys of a cryptocurrency address are physically printed out. These keys are often displayed as QR codes, along with respective alphanumeric strings.
The hardware wallet is considered to be the safest option because in this case, your keys are never going beyond the physical device. The confirmations of all transactions are also coming straight to the device 📟.
Hot Wallets
Hot wallets, in their turn, are connected to the internet. This is the group for the rest of the wallets: desktop, mobile, and web ones.
Desktop and mobile wallets are rather similar. It is software that you install and use on the main device. Such a program encrypts the keys with a password and keeps them on the device storage itself. When it’s time to sign a transaction, it takes out the encrypted version from the storage, decrypts the private key, signs the transaction, sends it, and then “forgets” (by unloading it from RAM).
Web Wallets
With web wallets, things are a bit complicated. There are wallets in the form of a website or web app, which are hosted under a domain (hereinafter “web wallet”), and wallets in the form of a browser extension (i.e. an addition to the browser). It makes a huge difference. They have different mechanisms under their hoods.
Let’s start with obvious weak points of all hot wallets:
- Storage. Its data is encrypted. However, it is already part of “success”. Usually, the access for the storage can be gained by other programs with a higher level of access installed on the same device as the wallet, namely viruses.
- Memory. It contains at least all keys which pop up from time to time. The majority of wallets also store your password or its hash to avoid the necessity of asking for them every time. Access to memory is usually gained in the same way, by viruses.
As shown, you can sleep in peace if you will follow the rules of “digital hygiene”. But everything is different in the case of web wallets.
You can use web wallets to gain access to the blockchain via a browser’s interface without downloading or installing third-party software. However, they have an array of downsides:
- Web wallets’ storage is the browser localStorage. It is NOT safe since it is located at the same scope as any JavaScript of the web page. Click here for details: https://dev.to/rdegges/please-stop-using-local-storage-1i04.
- Sometimes keys may be copied directly to the interface. This weak point is even more dangerous. A lot of browser extensions are managing your web page, and they may accidentally (or not accidentally) take the keys for themselves.
- Fishing Attacks. A phishing attack is a scam hackers use to steal personal information like usernames and passwords. It looks like this:
Bob is working on his laptop with several tabs open in his browser. He unlocks his wallet to make a transaction. An attacker uses the open tabs to see that Bob is using the wallet. The attacker sends Bob a pop-up message saying that his transaction has failed. This happens sometimes so Bob isn’t worried too much. He enters his password to re-send the transaction. The attacker now has access to Gene’s wallet.
- Browser access. Your browser won’t receive access to your private codes but it still may gather information on when and how you use the app.
Why ThanosWallet is more secure?
ThanosWallet is the web (browser) extension. Its mechanisms under the hood differ from online wallets’ ones.
- Web Extension API has a separate thread, Background Script. It means that it is isolated from everything. It is a separate process on your computer that is being launched under the authority of the browser.
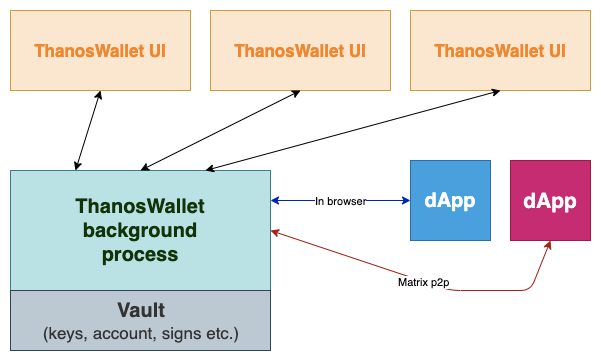
- Web Extensions has its special storage which is hidden from everyone except for the extension itself.
- ThanosWallet interface is also isolated from everything.
One more advantage of our wallet is the availability of a new standard for interaction with decentralized applications, namely tzip10. It is more protected from phishing attacks. Here are more details: https://www.walletbeacon.io
Thereby, we consider that ThanosWallet can be partially equated to Desktop and Mobile wallets 🔒.
Conclusion
- Hardware wallets are the safest;
- Web wallets (online) have more several weak points than other hot wallets;
- ThanosWallet is rather safe and protected.
What’s new in ThanosWallet? (development update):

🔒 Security improvement: new encryption and storage strategy. Read more about this above;
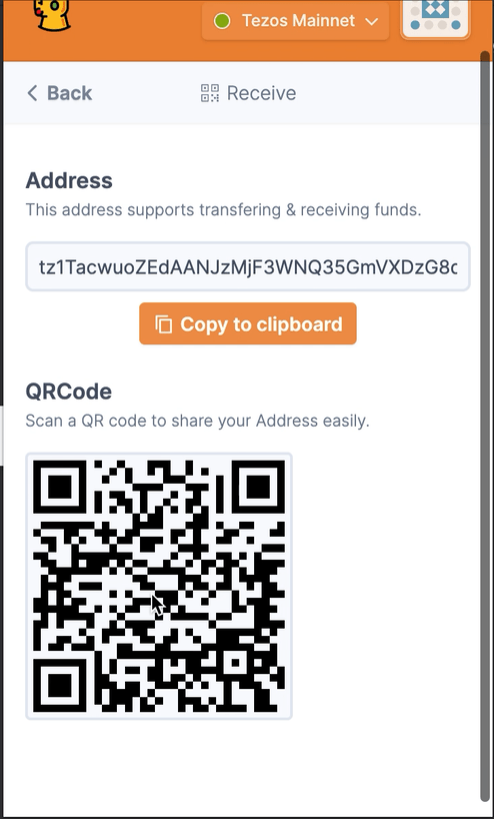
🍬😍 New interface for the popup page(is located in browser toolbar)
👥 Multi-accounting with different account types: HD Account(generated from root seed phrase) and Imported Account
💸 Basic explore(home) page layout with account stats and control actions
💳 Receive page with QR Code
🎛️ Settings page with wallet Seed Phrase revealing
Now everything is under development. We do not make official releases intentionally until we test everything. Expect the first alpha release at the end of March 🚀.
The project is hosted on Github: https://github.com/madfish-solutions/thanos-wallet
Don’t hesitate to star it⭐️
Subscribe for updates
Facebook and Twitter of course Medium 🙂
https://tezos.org.ua/ — Tezos Ukraine community website
https://twitter.com/UkraineTezos — Tezos Ukraine twitter